

Midnight Protocol is a tactical, turn-based RPG developed by LuGus Studios, released in October of 2021, that sees the player assume the role of a hacker known as “Data”. Just before the events of the game, another hacker, known as Kraken, released Data’s identity, and they were detained for a data breach, though got released for lack of evidence. The player picks up just after Data’s release, as they work with their associates to find out who doxxed them, as well as execute other jobs that come their way.
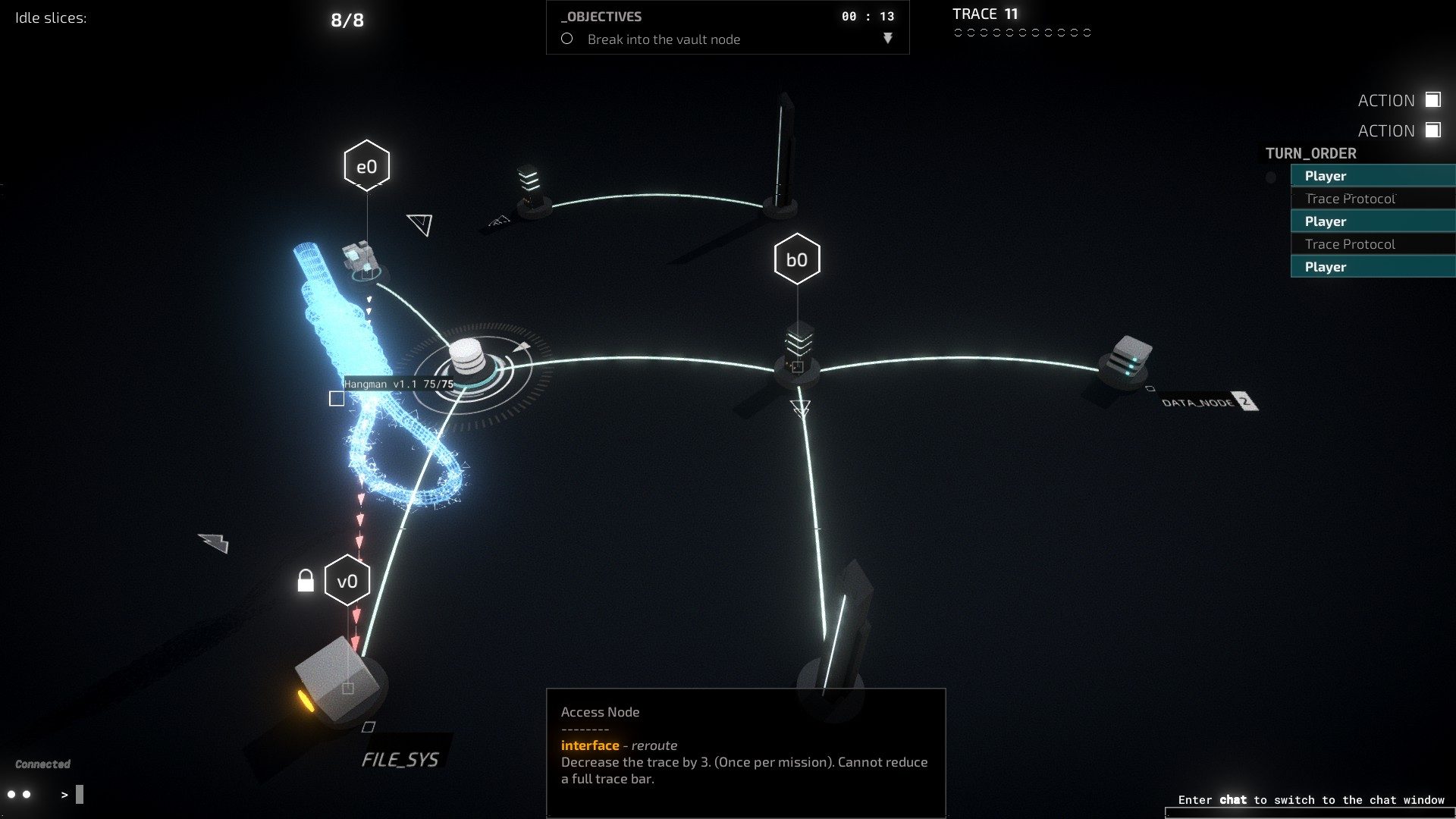
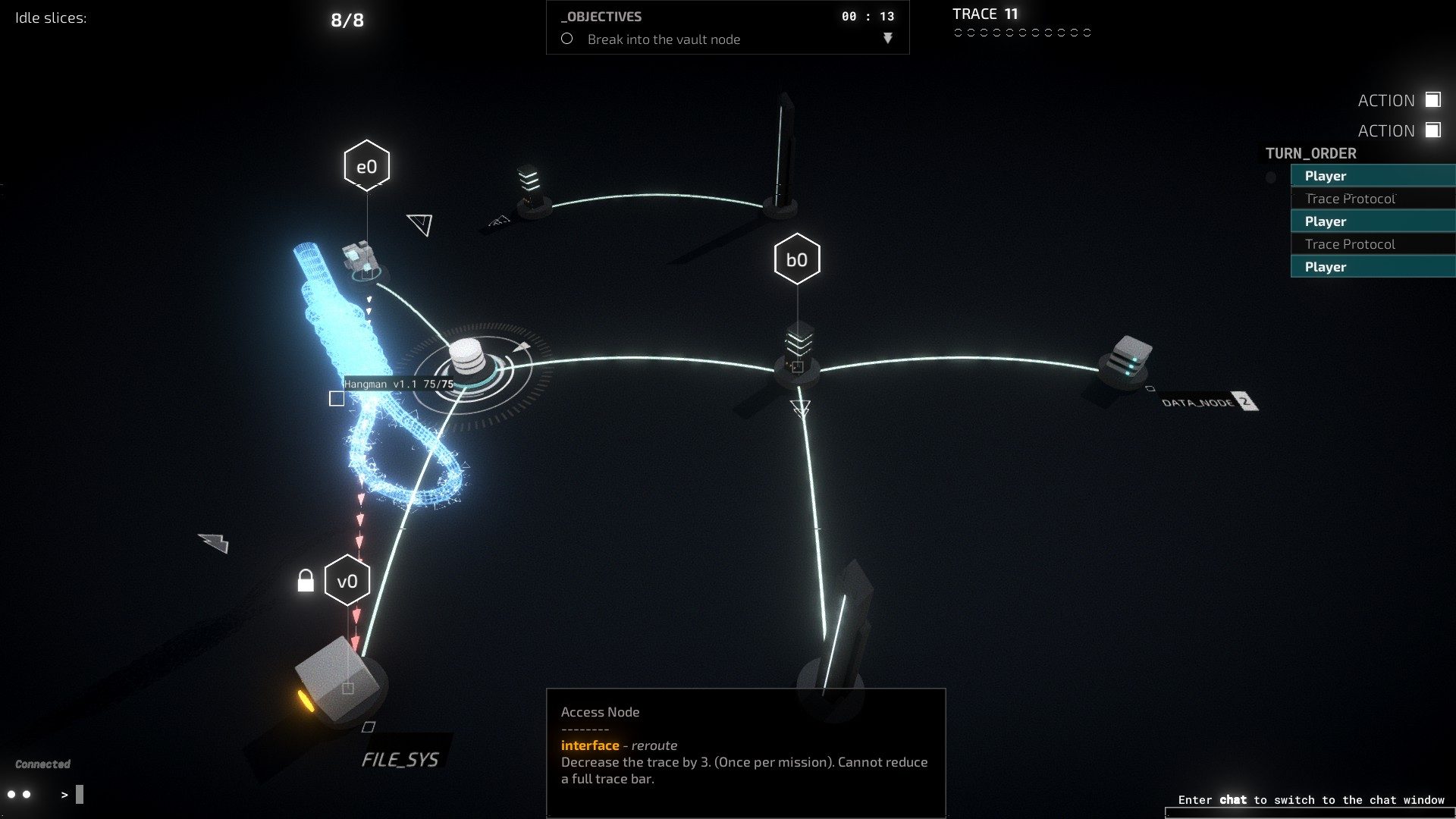
The game centers around its hacking mechanic, which has the player strategically navigate a board in order to complete the goals of a mission. Tasks often center around stealing data, stealing money, and planting viruses, among other goals. Players complete these tasks by moving around between a series of interconnected nodes, each with their own function (data nodes have data, financial nodes have money, etc.), as they try to avoid a tracer program aiming to kick them off of the network or other NPC players, called SysOps, who move around the board trying to stop them. Other obstacles, called ICE exist as various barriers meant to stop or slow down the player. The player deals with all of these by using different programs (which are essentially special abilities) to take down ICE, hide from SysOps, and accomplish their goals.
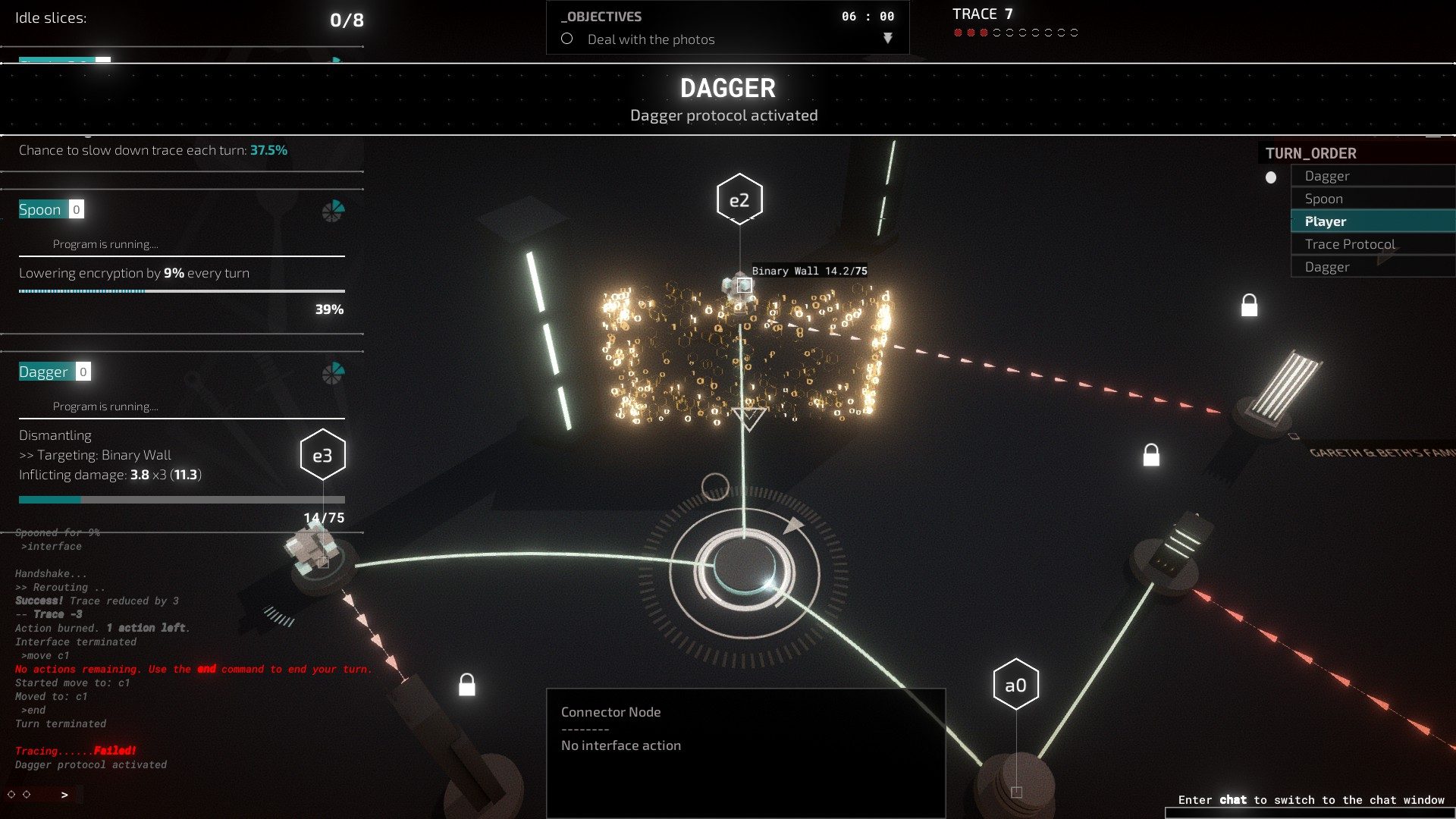
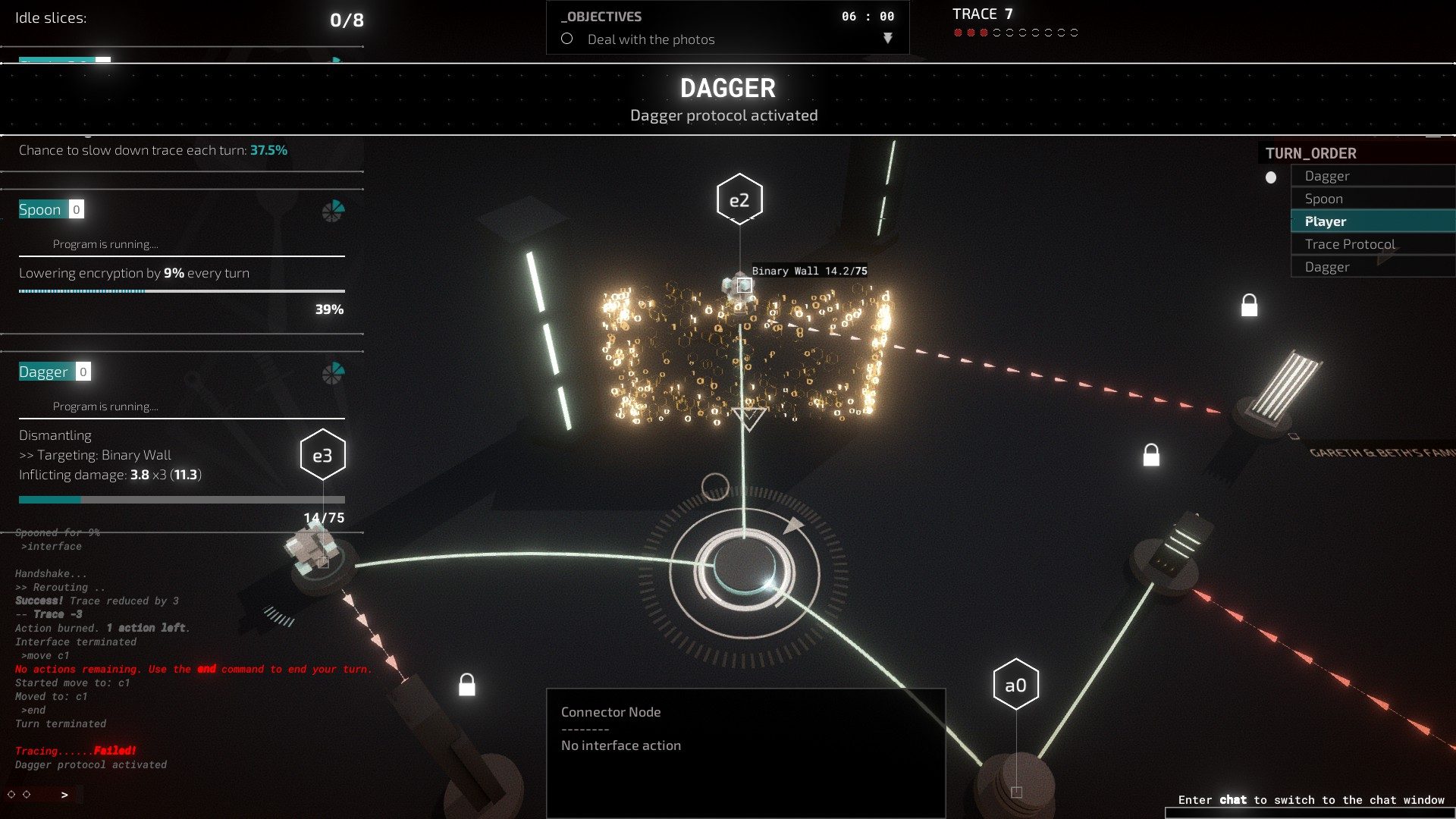
Actually explaining the gameplay makes it sound really complicated because everything in Midnight Protocol comes buried under layers of computer science ideas and hacker-style words, but the game, really, is a turn-based board game. That’s not to take away from the gameplay though, because the actual strategy of the game is a lot of fun. Trying to find efficient routes to the nodes you need to get to, finding out where the ICE are, and avoiding the tracer programs and SysOps is engaging and dynamic. Especially on the more complex levels with more nodes, a SysOp, and mechanics like Leviathan programs, the strategy happens both on a macro level, where you plan your opening, choose which programs you want for the level, and find the ICE, but also on a micro level, as you need to react turn-by-turn to the what the computer does as well in order to stop you.
The only major issue with the gameplay is its reliance on randomness. The primary “enemy” in the game, the Tracer program, works by trying to locate you at the end of every turn, but whether or not it locates you is based on a probability. You can use a cloaking program to lower the Tracer’s chance of finding you, but sometimes you just get bad luck. Even if the cloaking program reduces the Tracer’s chance of finding you by 50+%, sometimes it just finds you three, four, five times in a row, which, on some levels, essentially guarantees you’ll fail. Other times, you can have Cloak running on the lowest level and you’ll still evade the Tracer program several turns in a row. This doesn’t even account for the way that randomness impacts what AI SysOps do. Sometimes a SysOp will effortlessly clear the gap between you and it, as though it knew your exact location (which it generally doesn’t), and other times it will move to a node, immediately move back to its original node, and end its turn. Evading a SysOp, at times, amounts to little more the business as usual, with brief moments of panic as you have to fend off a hapless SysOp every few turns. I should note that while generally, trying to predict a SysOp’s movements is futile at best, admittedly sometimes you’ll predict so perfectly that you’ll feel like a real hacker, which can make these moments worth it.
In addition to the RNG sometimes making it impossible to beat a level no matter how competent you are, you generally don’t know ahead of time where the ICE programs are or what they are. Their placement isn’t random, but unless you have a special piece of hardware unlocked later in the game, your first time in a level is an absolute crapshoot where you basically just have to move and pray that you don’t fling yourself into an ICE program. All of these factors essentially require you to play some more difficult levels at least once or twice just to have enough information to actually beat it. These minutes spend replaying things really add up, especially when some missions can take upwards of twenty minutes to finish.
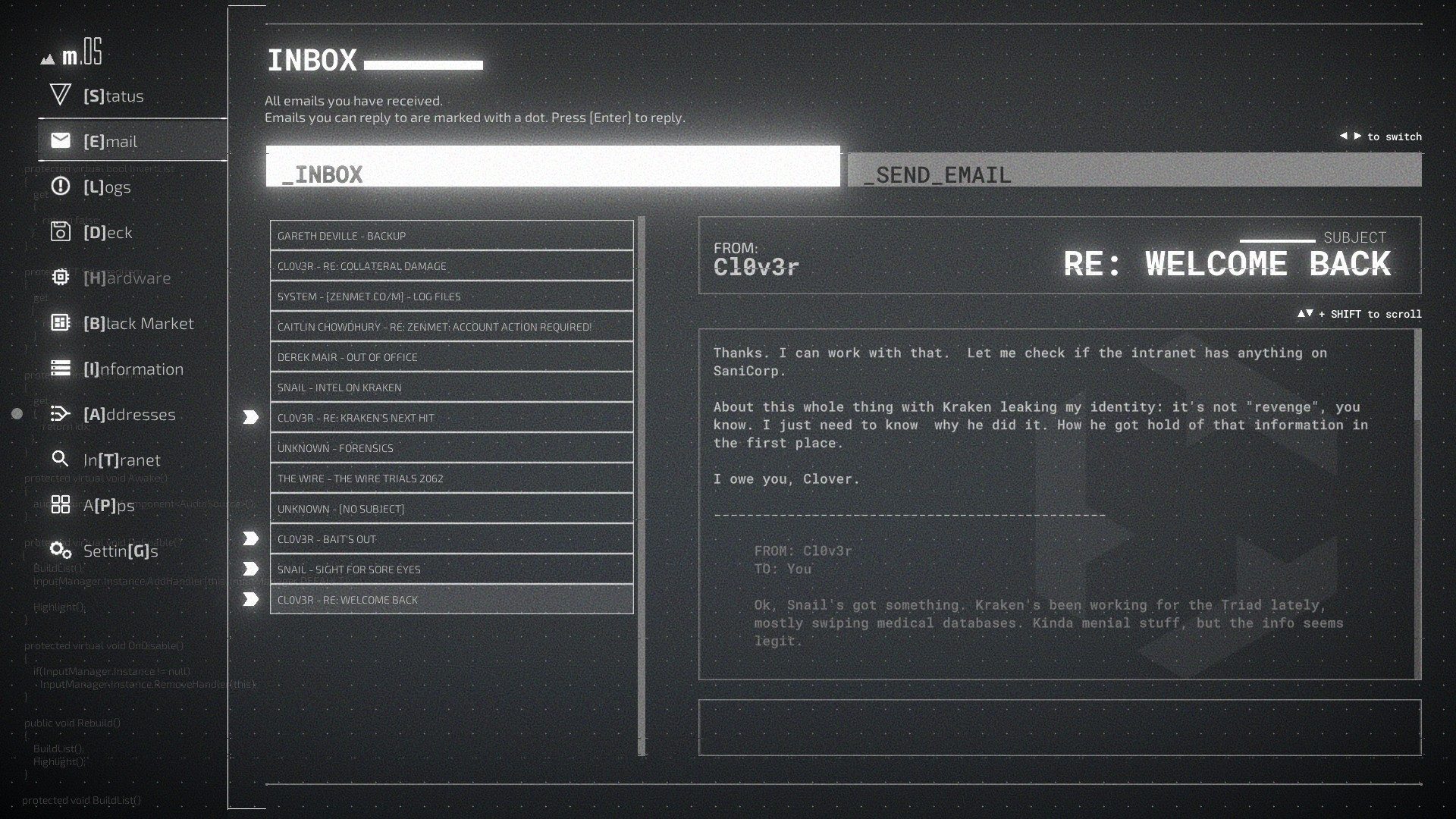
Outside of these missions, the rest of Midnight Protocol exists in a series of menus, designed to emulate a desktop. Much of the story happens in the Email tab, where you communicate with other characters, receive new jobs, and learn about the world. The Logs tab holds all of the mission information, and then you can manage your programs and hardware using the Deck, Hardware, and Black Market tabs. You actually choose with missions to play in the Addresses tab, though. There are a few other tabs, but these are the main ones, and the game has you spend a little too much time in them for my liking. Especially when it comes to the story contained in the Email and Logs tabs, the game has so much text to read, but it’s basically all optional. I found myself just rapidly clicking through the dialogues, emails, and logs to get back to the game, but this caused a bit of an issue as I quickly lost all reference for what I happening in the game, making the missions abstract and hard to get engaged with.
For someone really into hacking games, the menus won’t get too in the way of the experience, but for a casual player or someone less invested in the whole “hacker” motif, the amount of reading required to experience the story and the visual simplicity (all of the story happens in menus and all the missions look more or less the same) can make the game hard to really get into. The gameplay, while it has its issues, is pretty engaging, and definitely will grab people, especially people more into the style and type of game, but it just doesn’t have a lot else beyond that. The game, for what it is, is well-executed, but, and perhaps this is just a consequence of this type of game, it lacks a lot of the components that would capture someone not already invested in the game.
Score: 6 out of 10
Reviewed on PC
